| Lesson 9 | Specifying Protocols |
| Objective | Define modern remote and Web system protocols |
Define Modern Remote and Web System Protocols
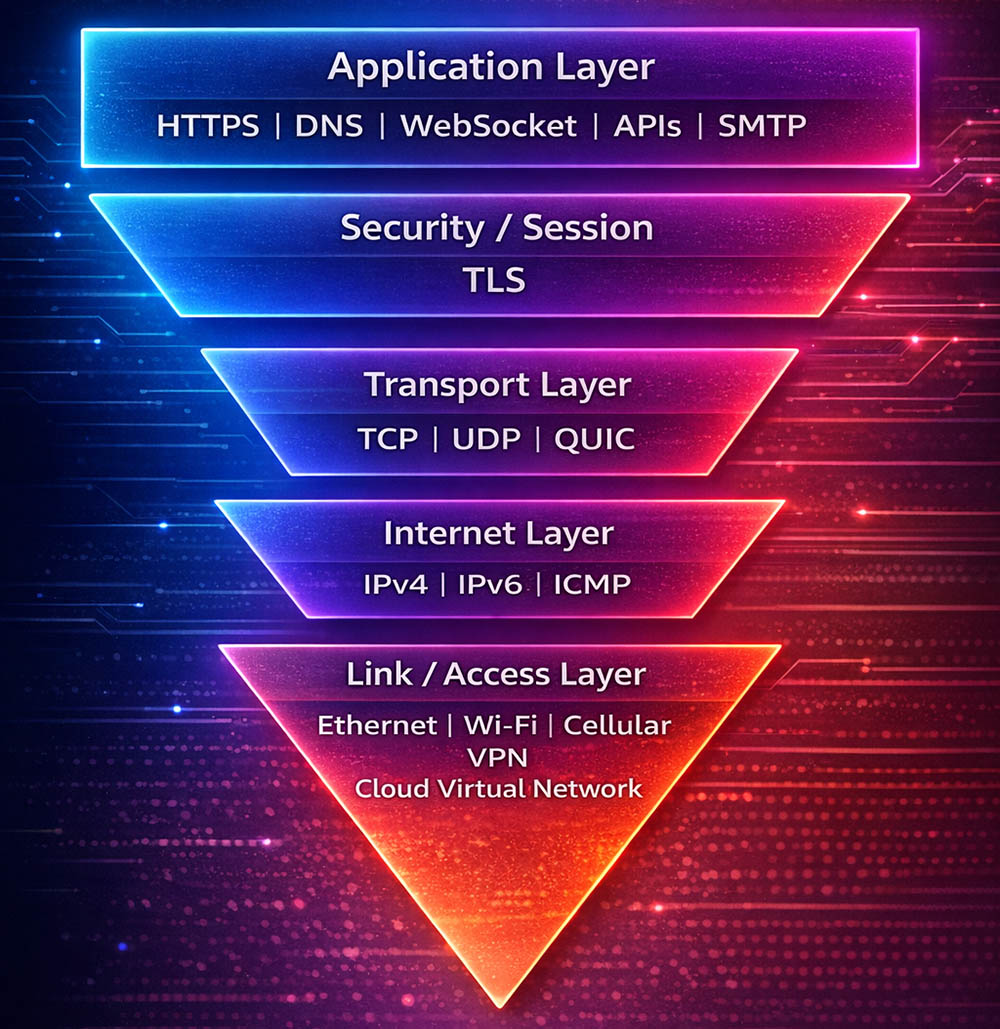
A modern website does not operate through a single protocol. Instead, it depends on a coordinated set of protocol layers that move requests, responses, sessions, names, addresses, and encrypted data between remote systems. A browser on a phone, tablet, laptop, or desktop sends requests across local and wide-area networks to remote servers, APIs, storage services, and cloud-hosted applications. Those requests travel through a layered communications model in which each layer performs a distinct role. Collectively, those roles allow a user to type a URL, locate a remote host, establish a secure connection, send a request, and receive a response such as HTML, JSON, images, video, or application data.
In older web-development discussions, the protocol stack was often simplified to a short list such as HTTP, FTP, TCP, UDP, and IP. That older presentation was useful as an introduction, but it no longer describes the full path used by modern web systems. In 2026, a realistic remote-system discussion must include application protocols such as HTTPS and DNS, security protocols such as TLS, transport choices such as TCP, UDP, and QUIC, internet-layer protocols such as IPv4 and IPv6, and access technologies such as Ethernet, Wi-Fi, cellular networking, VPNs, and cloud virtual networks.
The updated diagram for this lesson reflects that broader and more accurate view. Rather than treating remote access as a narrow concept associated with dial-up or legacy serial links, the figure shows how a modern remote system communicates through five interacting layers. These layers do not compete with one another. They cooperate. The application layer delivers services, the security layer protects data, the transport layer manages delivery behavior, the internet layer handles addressing and routing, and the link/access layer moves traffic across the underlying physical or virtual network.
In older web-development discussions, the protocol stack was often simplified to a short list such as HTTP, FTP, TCP, UDP, and IP. That older presentation was useful as an introduction, but it no longer describes the full path used by modern web systems. In 2026, a realistic remote-system discussion must include application protocols such as HTTPS and DNS, security protocols such as TLS, transport choices such as TCP, UDP, and QUIC, internet-layer protocols such as IPv4 and IPv6, and access technologies such as Ethernet, Wi-Fi, cellular networking, VPNs, and cloud virtual networks.
The updated diagram for this lesson reflects that broader and more accurate view. Rather than treating remote access as a narrow concept associated with dial-up or legacy serial links, the figure shows how a modern remote system communicates through five interacting layers. These layers do not compete with one another. They cooperate. The application layer delivers services, the security layer protects data, the transport layer manages delivery behavior, the internet layer handles addressing and routing, and the link/access layer moves traffic across the underlying physical or virtual network.
The Web Depends on Layered Communication
The World Wide Web is still built on the TCP/IP family, but the phrase TCP/IP now needs a more careful explanation. It refers not only to the Transmission Control Protocol and the Internet Protocol, but also to the broader family of standards and behaviors that enable networked communication. A remote web application works because naming, routing, encryption, transport, and application messaging all work together in sequence.
When a user visits a website, the process usually begins with a DNS lookup. DNS translates a human-friendly domain name into an IP address or other service endpoint information. Once the remote system is identified, the client establishes a network path over the internet. Depending on the application and protocol version, the client may build a secure TLS session over TCP, or it may use HTTP/3, which runs over QUIC and UDP. After the session is established, the browser sends an HTTPS request and receives a response that may contain HTML, CSS, JavaScript, images, fonts, API payloads, and caching directives.
This layered model is important because it explains what happens when something fails. If DNS fails, the remote system cannot be located. If TLS negotiation fails, the secure session cannot be established. If routing fails at the IP layer, packets cannot reach the destination. If the access layer has weak Wi-Fi coverage, unstable cellular service, or a misconfigured VPN, the application may appear slow or unavailable even though the web server itself is functioning correctly.
A byte stream still matters in networking, but modern web development requires more than a low-level description of bytes, packets, and checksums. Developers, site owners, and system architects need to understand how protocol layers map to practical web behavior: encrypted browsing, API calls, CDN delivery, mobile access, cloud load balancing, remote administration, and observability across distributed systems.
When a user visits a website, the process usually begins with a DNS lookup. DNS translates a human-friendly domain name into an IP address or other service endpoint information. Once the remote system is identified, the client establishes a network path over the internet. Depending on the application and protocol version, the client may build a secure TLS session over TCP, or it may use HTTP/3, which runs over QUIC and UDP. After the session is established, the browser sends an HTTPS request and receives a response that may contain HTML, CSS, JavaScript, images, fonts, API payloads, and caching directives.
This layered model is important because it explains what happens when something fails. If DNS fails, the remote system cannot be located. If TLS negotiation fails, the secure session cannot be established. If routing fails at the IP layer, packets cannot reach the destination. If the access layer has weak Wi-Fi coverage, unstable cellular service, or a misconfigured VPN, the application may appear slow or unavailable even though the web server itself is functioning correctly.
A byte stream still matters in networking, but modern web development requires more than a low-level description of bytes, packets, and checksums. Developers, site owners, and system architects need to understand how protocol layers map to practical web behavior: encrypted browsing, API calls, CDN delivery, mobile access, cloud load balancing, remote administration, and observability across distributed systems.
Application Layer Protocols
The top layer in the figure is the Application Layer. This is the layer most visible to users and developers because it includes the protocols that directly support web and messaging services.
HTTPS is now the standard protocol for delivering websites and web applications. It combines HTTP semantics with TLS encryption so that requests and responses are protected in transit. In practice, HTTPS is the default for production websites, e-commerce systems, SaaS platforms, login workflows, content delivery networks, and most API endpoints.
DNS remains essential because remote systems are usually reached through domain names rather than raw IP addresses. DNS is not merely a lookup tool; it is also part of traffic steering, failover design, service discovery, and content distribution.
WebSocket supports persistent, full-duplex communication between client and server. This is useful for dashboards, collaborative tools, chat systems, notifications, live market feeds, and monitoring consoles.
APIs represent a major part of modern web architecture. A browser-based front end often communicates with remote API services that expose business logic, authentication, search, payment processing, analytics, and database-backed operations.
SMTP is included because remote systems frequently send transactional email such as password-reset links, verification messages, form notifications, receipts, and monitoring alerts.
Older lessons often emphasized FTP as a major high-level web protocol. FTP still exists, but it is no longer a leading example for modern public-facing web systems. In current deployments, secure file movement is more likely to involve HTTPS-based interfaces, SFTP, object storage upload workflows, CI/CD pipelines, or managed cloud transfer tools.
HTTPS is now the standard protocol for delivering websites and web applications. It combines HTTP semantics with TLS encryption so that requests and responses are protected in transit. In practice, HTTPS is the default for production websites, e-commerce systems, SaaS platforms, login workflows, content delivery networks, and most API endpoints.
DNS remains essential because remote systems are usually reached through domain names rather than raw IP addresses. DNS is not merely a lookup tool; it is also part of traffic steering, failover design, service discovery, and content distribution.
WebSocket supports persistent, full-duplex communication between client and server. This is useful for dashboards, collaborative tools, chat systems, notifications, live market feeds, and monitoring consoles.
APIs represent a major part of modern web architecture. A browser-based front end often communicates with remote API services that expose business logic, authentication, search, payment processing, analytics, and database-backed operations.
SMTP is included because remote systems frequently send transactional email such as password-reset links, verification messages, form notifications, receipts, and monitoring alerts.
Older lessons often emphasized FTP as a major high-level web protocol. FTP still exists, but it is no longer a leading example for modern public-facing web systems. In current deployments, secure file movement is more likely to involve HTTPS-based interfaces, SFTP, object storage upload workflows, CI/CD pipelines, or managed cloud transfer tools.
Security and Session Layer
The second layer in the figure is Security / Session, represented by TLS. In a 2026 context, this layer deserves explicit attention because security is not optional. Remote systems routinely transmit credentials, session cookies, tokens, account information, financial data, API keys, and administrative traffic. TLS protects confidentiality and helps preserve message integrity while also supporting server authentication.
In older instructional material, security was sometimes treated as an add-on or a later enhancement. That is no longer acceptable for production web architecture. Secure-by-default communication is a baseline expectation for websites, APIs, CDNs, cloud platforms, reverse proxies, and managed services.
TLS also plays a practical operational role in cloud infrastructure. Load balancers may terminate TLS connections before forwarding requests to application servers. CDNs may maintain separate TLS sessions between the user and the edge, and between the edge and the origin. Internal service-to-service communication may also be encrypted, especially in regulated, enterprise, or zero-trust environments.
In older instructional material, security was sometimes treated as an add-on or a later enhancement. That is no longer acceptable for production web architecture. Secure-by-default communication is a baseline expectation for websites, APIs, CDNs, cloud platforms, reverse proxies, and managed services.
TLS also plays a practical operational role in cloud infrastructure. Load balancers may terminate TLS connections before forwarding requests to application servers. CDNs may maintain separate TLS sessions between the user and the edge, and between the edge and the origin. Internal service-to-service communication may also be encrypted, especially in regulated, enterprise, or zero-trust environments.
Transport Layer Protocols
The third layer is the Transport Layer, which includes TCP, UDP, and QUIC.
TCP remains important because it provides ordered, reliable delivery. Many traditional web interactions, database sessions, administrative tools, and application back-end connections depend on TCP.
UDP does not provide the same built-in delivery guarantees as TCP, but it is useful in scenarios where low latency is more important than retransmission overhead. Real-time media, signaling systems, and some performance-sensitive networking models use UDP as the base transport.
QUIC is one of the key modern additions that distinguishes a 2026 protocol discussion from an older one. QUIC runs over UDP and is used by HTTP/3. It improves connection setup behavior, supports stream multiplexing, and is designed to perform well in conditions such as mobile-network changes, high-latency paths, and encrypted modern web delivery.
This matters for remote systems because a user may begin a session on Wi-Fi, move to cellular access, and continue interacting with a cloud-hosted application. A modern transport discussion must therefore include mobility, latency, resilience, and encrypted performance, not merely the old distinction that TCP is reliable while UDP is faster.
TCP remains important because it provides ordered, reliable delivery. Many traditional web interactions, database sessions, administrative tools, and application back-end connections depend on TCP.
UDP does not provide the same built-in delivery guarantees as TCP, but it is useful in scenarios where low latency is more important than retransmission overhead. Real-time media, signaling systems, and some performance-sensitive networking models use UDP as the base transport.
QUIC is one of the key modern additions that distinguishes a 2026 protocol discussion from an older one. QUIC runs over UDP and is used by HTTP/3. It improves connection setup behavior, supports stream multiplexing, and is designed to perform well in conditions such as mobile-network changes, high-latency paths, and encrypted modern web delivery.
This matters for remote systems because a user may begin a session on Wi-Fi, move to cellular access, and continue interacting with a cloud-hosted application. A modern transport discussion must therefore include mobility, latency, resilience, and encrypted performance, not merely the old distinction that TCP is reliable while UDP is faster.
Internet Layer Protocols
The fourth layer is the Internet Layer, consisting of IPv4, IPv6, and ICMP.
IPv4 is still widely used across the public internet and private networks. It remains part of many production deployments, NAT environments, firewall policies, and monitoring tools.
IPv6 is increasingly important because address scale, cloud adoption, device growth, and modern ISP support all push networks toward dual-stack or IPv6-aware design. Any modern explanation of remote systems should acknowledge IPv6 rather than treating IPv4 as the only relevant addressing model.
ICMP supports network diagnostics and control messaging. While ordinary users may notice it mainly through tools such as ping or traceroute, administrators rely on ICMP-related behaviors when diagnosing reachability, latency, routing issues, and path failures.
A remote web system cannot function unless packets are properly addressed and routed. This layer therefore answers the question: how does traffic know where to go? Application protocols may define the service, but the internet layer provides the logical addressing and routing foundation that lets remote systems find one another across local networks, ISPs, data centers, and cloud environments.
IPv4 is still widely used across the public internet and private networks. It remains part of many production deployments, NAT environments, firewall policies, and monitoring tools.
IPv6 is increasingly important because address scale, cloud adoption, device growth, and modern ISP support all push networks toward dual-stack or IPv6-aware design. Any modern explanation of remote systems should acknowledge IPv6 rather than treating IPv4 as the only relevant addressing model.
ICMP supports network diagnostics and control messaging. While ordinary users may notice it mainly through tools such as ping or traceroute, administrators rely on ICMP-related behaviors when diagnosing reachability, latency, routing issues, and path failures.
A remote web system cannot function unless packets are properly addressed and routed. This layer therefore answers the question: how does traffic know where to go? Application protocols may define the service, but the internet layer provides the logical addressing and routing foundation that lets remote systems find one another across local networks, ISPs, data centers, and cloud environments.
Link and Access Layer
The fifth layer is the Link / Access Layer, which includes Ethernet, Wi-Fi, Cellular, VPN, and Cloud Virtual Network.
This is another area where modern teaching must move beyond older assumptions. Legacy lessons often described remote access in terms of dial-up, SLIP, PPP, or dedicated leased lines such as T1 and T3. Those technologies are historically significant, but they no longer represent the normal deployment environment for modern web projects.
Today, remote systems are commonly reached through broadband fiber, cable, enterprise Ethernet, Wi-Fi 6/7, 4G/5G cellular networks, SD-WAN overlays, VPN tunnels, and cloud provider virtual networks. The access path may include home internet, a mobile carrier, a branch office edge device, a CDN edge node, or a virtual private cloud segment inside AWS, Azure, or Google Cloud.
The inclusion of Cloud Virtual Network is especially important for this lesson. Modern websites are often deployed on infrastructure that is partly or entirely virtualized. A web server may run behind a cloud load balancer, connect to a managed database on a private subnet, access object storage through private endpoints, and expose only selected services to the public internet. In that environment, the access layer is no longer just “the wire.” It includes virtual switching, subnet design, route tables, security groups, and private connectivity patterns inside the cloud.
This is another area where modern teaching must move beyond older assumptions. Legacy lessons often described remote access in terms of dial-up, SLIP, PPP, or dedicated leased lines such as T1 and T3. Those technologies are historically significant, but they no longer represent the normal deployment environment for modern web projects.
Today, remote systems are commonly reached through broadband fiber, cable, enterprise Ethernet, Wi-Fi 6/7, 4G/5G cellular networks, SD-WAN overlays, VPN tunnels, and cloud provider virtual networks. The access path may include home internet, a mobile carrier, a branch office edge device, a CDN edge node, or a virtual private cloud segment inside AWS, Azure, or Google Cloud.
The inclusion of Cloud Virtual Network is especially important for this lesson. Modern websites are often deployed on infrastructure that is partly or entirely virtualized. A web server may run behind a cloud load balancer, connect to a managed database on a private subnet, access object storage through private endpoints, and expose only selected services to the public internet. In that environment, the access layer is no longer just “the wire.” It includes virtual switching, subnet design, route tables, security groups, and private connectivity patterns inside the cloud.
Outdated Remote Access Models Versus Contemporary Web Deployment
Older instructional materials often associated remote communication with dial-up connectivity, serial-line access, PPP, PPTP, and SLIP. These concepts belong to the history of networking, and some are still worth knowing for context, but they should not dominate a modern lesson objective.
Dial-up internet and serial-line models are obsolete for mainstream web deployment. T1 and T3 circuits are legacy business connectivity options that have largely been replaced by broadband fiber, cable access, direct cloud connectivity, and software-defined networking. PPTP is historically notable but no longer a preferred VPN technology for secure modern environments. SLIP is now primarily of historical interest.
A contemporary website deployment project is more likely to involve broadband WAN access, HTTPS everywhere, CDN distribution, reverse proxies, TLS certificate management, API gateways, cloud firewalls, containerized services, virtual networks, edge caching, and mobile-first optimization.
That does not mean older protocols should be erased from history. It means the lesson should distinguish between historical remote-access technologies and the protocol layers that actually support current web systems. For a student, developer, or site owner, that distinction is critical because architectural decisions now depend on performance, encryption, scalability, availability, and cloud integration.
Dial-up internet and serial-line models are obsolete for mainstream web deployment. T1 and T3 circuits are legacy business connectivity options that have largely been replaced by broadband fiber, cable access, direct cloud connectivity, and software-defined networking. PPTP is historically notable but no longer a preferred VPN technology for secure modern environments. SLIP is now primarily of historical interest.
A contemporary website deployment project is more likely to involve broadband WAN access, HTTPS everywhere, CDN distribution, reverse proxies, TLS certificate management, API gateways, cloud firewalls, containerized services, virtual networks, edge caching, and mobile-first optimization.
That does not mean older protocols should be erased from history. It means the lesson should distinguish between historical remote-access technologies and the protocol layers that actually support current web systems. For a student, developer, or site owner, that distinction is critical because architectural decisions now depend on performance, encryption, scalability, availability, and cloud integration.
How the Layers Interact in a Cloud Scenario
Consider a common 2026 example. A user opens a browser on a smartphone connected through Wi-Fi or cellular data. The user enters a domain name for a cloud-hosted website. DNS resolves the name to a CDN edge or load balancer address. The browser establishes a secure TLS session, perhaps using HTTP/3 over QUIC. The request passes through internet routing, arrives at an edge service, and is then forwarded across a cloud virtual network to an application tier. That application tier may call internal APIs, query a database, retrieve files from object storage, and return a response.
In that one transaction, every layer in the figure participates:
In that one transaction, every layer in the figure participates:
- The Application Layer carries the HTTPS request and any API interactions.
- The Security / Session Layer protects the session with TLS.
- The Transport Layer uses TCP or QUIC/UDP depending on the protocol stack in use.
- The Internet Layer routes packets across public and private IP networks.
- The Link / Access Layer includes the user’s Wi-Fi or cellular path and the cloud provider’s virtual network.
Conclusion
To define modern remote and web system protocols is to recognize that remote communication is no longer a narrow topic limited to a few legacy connection methods. A modern remote system depends on layered protocols that support naming, encryption, delivery, routing, and access across both physical and virtual infrastructure.
The updated figure for this lesson presents a more accurate 2026 model than the older stack based only on HTTP, FTP, UDP, TCP, and IP. Today’s web systems operate through application protocols such as HTTPS, DNS, WebSocket, APIs, and SMTP; security through TLS; transport through TCP, UDP, and QUIC; internet-layer addressing through IPv4 and IPv6; and access through Ethernet, Wi-Fi, cellular, VPNs, and cloud virtual networks.
Understanding these layers helps explain how a remote browser reaches a remote server, how cloud-hosted applications deliver content securely, and why network design still matters in website deployment. In the next lesson, the network requirements necessary to meet business goals for a website development project will be discussed.
The updated figure for this lesson presents a more accurate 2026 model than the older stack based only on HTTP, FTP, UDP, TCP, and IP. Today’s web systems operate through application protocols such as HTTPS, DNS, WebSocket, APIs, and SMTP; security through TLS; transport through TCP, UDP, and QUIC; internet-layer addressing through IPv4 and IPv6; and access through Ethernet, Wi-Fi, cellular, VPNs, and cloud virtual networks.
Understanding these layers helps explain how a remote browser reaches a remote server, how cloud-hosted applications deliver content securely, and why network design still matters in website deployment. In the next lesson, the network requirements necessary to meet business goals for a website development project will be discussed.
Protocols and Addresses Quiz
Click the quiz link below to check your learning of protocols and addresses.
Protocols Addresses - Quiz
Protocols Addresses - Quiz