| Lesson 5 | Server Security |
| Objective | Designing e-commerce system security at the server level using modern best practices |
Server-Level Components for E-Commerce Security
- Database Servers: Host databases on private subnets or isolated VLANs with no direct Internet access. Require encrypted connections (TLS 1.3) and use IAM-based authentication with least-privilege roles. Keep database services patched, disable unused features, and store encryption keys in a centralized KMS or HSM.
- Application & Middleware: Secure application servers, API gateways, and middleware with strict authentication and authorization policies. Use mTLS or OIDC for service-to-service communication. Apply dependency scanning, maintain a Software Bill of Materials (SBOM), and pull all secrets from a managed vault. Disable default admin endpoints and enforce input validation for all APIs.
- Web Servers: Place a reverse proxy or WAF in front of web servers to filter malicious traffic and enforce TLS 1.3 with strong ciphers. Remove unused modules, disable directory listing, set strict HTTP security headers, and keep services updated. Example HSTS header:
Segment web server resources from application logic and static content using separate infrastructure or containers.Strict-Transport-Security: max-age=31536000; includeSubDomains; preload - File Transfer Services: Replace legacy FTP with secure alternatives such as SFTP, HTTPS uploads, or managed FTPS with modern encryption. Require authenticated accounts with least-privilege access, use chroot/jail environments, and scan all uploaded files for malware before processing. Log all transfers and enable integrity verification with checksums.
Secure File Transfer Practices
For projects that require large file exchanges, use secure protocols such as SFTP or HTTPS with pre-signed URLs. Avoid anonymous access. When partner or client access is necessary, create dedicated, expiring credentials with IP allowlists. Quarantine all uploads for antivirus and content policy scanning before release into production. Maintain full audit logs for compliance and forensics.
Disable or replace insecure legacy protocols. If FTPS is required for compatibility, ensure TLS 1.3 is enforced and that weak ciphers are disabled. Avoid revealing server version banners, but prioritize rapid patching and minimal attack surface over obscurity.
Securing Resources
Modern network segmentation ensures that no single breach compromises the entire environment. Place the web and application tiers behind a reverse proxy or WAF. Use private networking (such as VPC peering or service mesh) between tiers, and do not expose database services publicly.
Implement intrusion detection and response (IDS/IPS or EDR/XDR) at key points in the architecture. Use centralized SIEM logging with tamper-evident storage. All communication between services should be encrypted and authenticated.
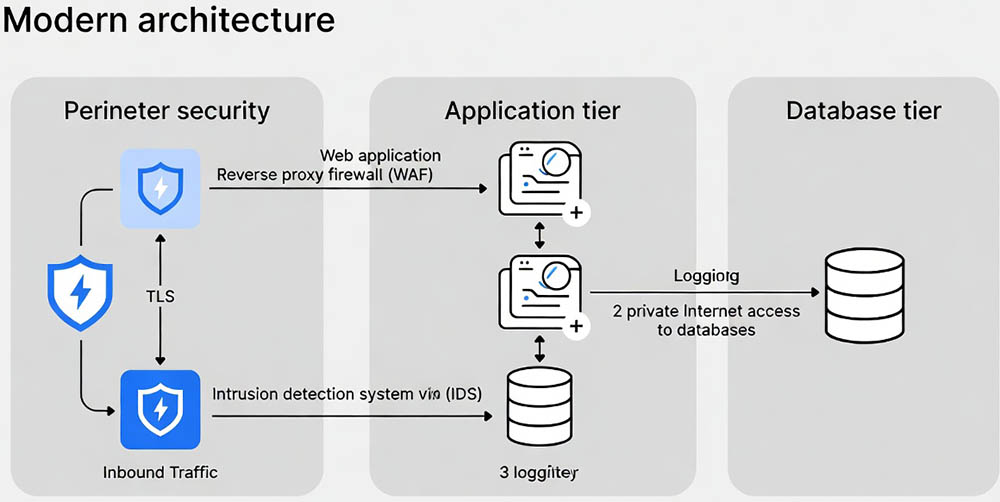
- Reverse proxy and WAF filter inbound traffic, enforce TLS, and block malicious requests before they reach the application tier.
- Application servers communicate with databases over private, encrypted channels. No direct Internet access to the database tier.
- Intrusion detection, logging, and continuous monitoring are in place across all tiers for real-time threat detection and response.
Email Servers
Simple Mail Transfer Protocol (SMTP): Secure email services are critical for protecting customer communications and transactional messages. Enforce SPF, DKIM, and DMARC (set to quarantine or reject) to prevent spoofing. Require TLS 1.3 for all message transfers and enable MTA-STS/TLS-RPT for delivery security. Use attachment sandboxing and phishing detection to protect end-users. Separate marketing and transactional email systems to reduce risk exposure.
Security Issues – Quiz
Security Issues – Quiz