CGI Scripts and Web Search Engines
No Web site can exist without adequate gateways to information stores and ways to provide active content.
CGI scripting, whether it is provided through PHP, ASP, perl, or any other method, is vital.
However, such solutions have traditionally invited hackers into e-commerce systems.
This is because many CGI implementations are left at their default settings.
Both Microsoft IIS and Allaire's Cold Fusion Server install with sample sites and searching services that are meant to provide helpful e-commerce hints. If left on the server, however, they can cause serious problems.
Hackers can use Microsoft's site searching engine, for example, to search the entire hard drive to find sensitive information.
Hackers have also exploited Cold Fusion sample code to obtain administrative or root access to the entire server. Although each of these products is quite powerful, you should take care that such CGI scripting solutions and search engines do not cause security problems.
Perl/CGI Variables
Both Microsoft IIS and Allaire's Cold Fusion Server install with sample sites and searching services that are meant to provide helpful e-commerce hints. If left on the server, however, they can cause serious problems.
Hackers can use Microsoft's site searching engine, for example, to search the entire hard drive to find sensitive information.
Hackers have also exploited Cold Fusion sample code to obtain administrative or root access to the entire server. Although each of these products is quite powerful, you should take care that such CGI scripting solutions and search engines do not cause security problems.
CGI scripts
The Common Gateway Interface was the first interface designed to provide developers with the capability to produce dynamic content on their Web sites.
With this introduction, suddenly pages began to transform from informative but stale HTML to active feedback environments.
The first search engines, registration sites, Webbased chat forums, and online database queries were implemented using CGI.
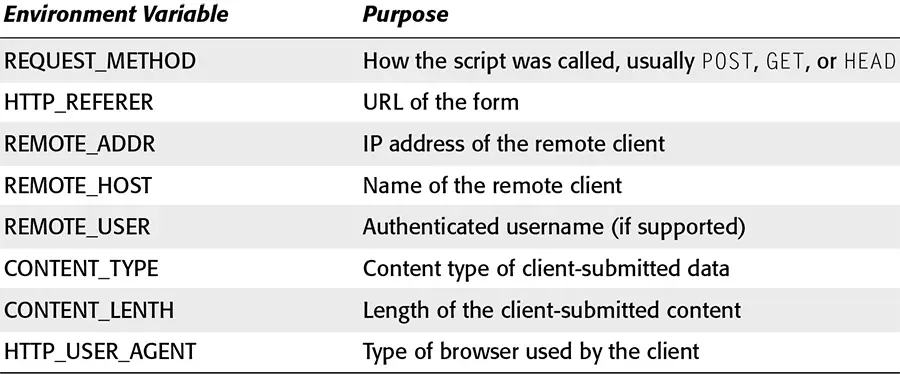
The execution component of a CGI script can be written in any programming language that can execute on the host machine (Perl, Python, Shell, C, C++, and so on). Because of its ability to parse text easily, Perl tends to be the most popular of the choices. To be most effective, this language should be able to read from the standard input stream, output to the standard output stream, and read environment variables. Examples of commonly used environment variables used in active content are listed in Table 4-3.
The execution component of a CGI script can be written in any programming language that can execute on the host machine (Perl, Python, Shell, C, C++, and so on). Because of its ability to parse text easily, Perl tends to be the most popular of the choices. To be most effective, this language should be able to read from the standard input stream, output to the standard output stream, and read environment variables. Examples of commonly used environment variables used in active content are listed in Table 4-3.
CGI scripts are located in a specified directory within a Web server (usually /cgi-bin). Although they are physically separated from sensitive system files, configuration errors can lead to access by malicious users.
Dropshipping