| Lesson 7 | Authentication |
| Objective | Identify authentication methods used in ecommerce |
Authentication Methods in ecommerce (Digital Signatures and MFA Explained)
In ecommerce, authentication and certification both play critical roles in securing online transactions, but they function differently. Authentication proves who the parties are to one another, and certification uses an intermediary for proof. Authentication through digital signatures is used in high-risk ecommerce transactions, as well as for the delivery of highly sensitive information, including software. Understanding both mechanisms — and the specific authentication methods available in 2026 — is essential for anyone designing or operating an ecommerce security system.
Authentication vs Certification — The Core Distinction
Authentication — Proving Who You Are
Authentication is the process of verifying the identity of the parties involved in a transaction — ensuring they are who they claim to be. In ecommerce, authentication operates at two levels simultaneously. Customer authentication verifies that the person initiating a purchase is the legitimate account holder — not an impostor using stolen credentials. Server authentication verifies that the website accepting the customer's payment is the legitimate merchant — not a phishing site designed to capture payment data. Both levels of authentication must succeed for a transaction to be trusted.
In the authentication process, the recipient of a message receives a digital signature. Because a correctly implemented digital signature cannot be forged without access to the signer's private key, the recipient can be confident of the sender's identity. Digital signatures provide both authentication (who sent the message) and non-repudiation (proof that cannot be denied) — the combination that makes them the mechanism of choice for high-value ecommerce transactions and sensitive information delivery.
In the authentication process, the recipient of a message receives a digital signature. Because a correctly implemented digital signature cannot be forged without access to the signer's private key, the recipient can be confident of the sender's identity. Digital signatures provide both authentication (who sent the message) and non-repudiation (proof that cannot be denied) — the combination that makes them the mechanism of choice for high-value ecommerce transactions and sensitive information delivery.
Certification — A Trusted Third Party Vouches for You
Certification involves a trusted third-party intermediary — a Certificate Authority (CA) — verifying the authenticity of entities involved in the transaction. In ecommerce, certification is primarily associated with the security of the website itself. When a customer visits an ecommerce site and sees the padlock symbol in the browser's address bar alongside an HTTPS URL, that padlock indicates that the website holds a TLS certificate issued by a trusted CA. The CA verified the identity of the ecommerce website's operator before issuing the certificate — providing the customer with third-party assurance that they are interacting with the legitimate merchant rather than a fraudulent impersonation.
The browser uses the TLS certificate to authenticate the site cryptographically: it verifies the certificate's digital signature against the CA's public key, confirms the domain name matches the certificate's subject, and checks that the certificate has not been revoked. This certificate-based verification prevents man-in-the-middle attacks by ensuring that no impersonator can present a fraudulent identity without possessing a certificate signed by a trusted CA — which they cannot obtain without legitimate ownership of the domain.
The browser uses the TLS certificate to authenticate the site cryptographically: it verifies the certificate's digital signature against the CA's public key, confirms the domain name matches the certificate's subject, and checks that the certificate has not been revoked. This certificate-based verification prevents man-in-the-middle attacks by ensuring that no impersonator can present a fraudulent identity without possessing a certificate signed by a trusted CA — which they cannot obtain without legitimate ownership of the domain.
Why ecommerce Needs Both
Authentication and certification address different threat surfaces. A valid TLS certificate (certification) proves the website is legitimate but says nothing about whether the customer logging in is the real account holder. Multi-factor authentication (authentication) proves the customer's identity but says nothing about whether the site they are authenticating to is genuine. An ecommerce platform that has strong customer authentication but an invalid or absent TLS certificate exposes customers to MitM attacks that intercept their credentials. A platform with a valid certificate but only password-based customer authentication is vulnerable to credential stuffing and account takeover. Both mechanisms are required simultaneously — which is why PCI DSS mandates both TLS for data-in-transit protection and strong customer authentication for account access.
The Digital Signature Process — Figure m5-7.1
Figure m5-7.1 shows the complete seven-step digital signature process — the mechanism by which authentication is implemented in high-risk ecommerce transactions. The diagram is organized in two rows: the gold zone (steps 1–3) shows what the sender does to create and sign the message; the amber transmission arrow carries the signed message across the network; the cyan zone (steps 4–6) shows what the receiver does to verify it; and the green zone (step 7) shows the verification outcome.
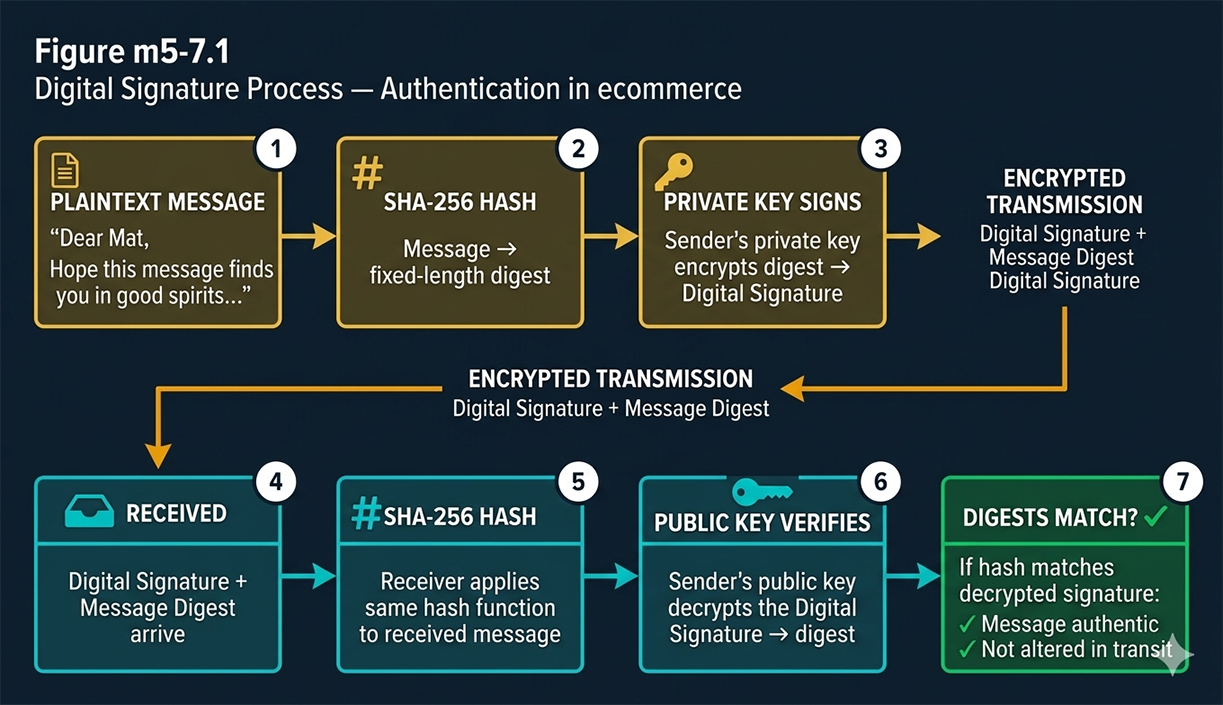
How Digital Signatures Work — Step by Step
Steps 1–3: The Sender Creates the Signature
A cryptographic algorithm uses a cipher to encrypt and decrypt plaintext messages. A cipher is a mathematical function; the keys are the numbers or values used in that mathematical function. Step 1 begins with the plaintext message — the original, human-readable content ("Dear Mat, Hope this message finds you in good spirits..."). In Step 2, the sender applies a hash function (SHA-256) to the plaintext, producing a fixed-length message digest — a unique fingerprint of the message content. Any change to the plaintext, even a single character, produces a completely different digest. In Step 3, the sender encrypts the digest with their private key, producing the digital signature. The private key is the element that makes the signature unforgeable: only the holder of the private key can produce a signature that the corresponding public key will verify. The resulting digital signature, combined with the message digest, is what gets transmitted.
Steps 4–5: Transmission and Message Digest at Receiver
The message is transmitted electronically — the digital signature and message digest travel alongside the message content across the network, encrypted by TLS for transport security. At the destination, Step 4 is receipt: the receiver receives the digital signature and message digest. In Step 5, the receiver independently applies the same SHA-256 hash function to the received message, producing their own message digest from the content they received. This independently computed digest is the comparison baseline — if the message was unaltered in transit, the receiver's hash of the received content must match the hash the sender computed before signing.
Steps 6–7: Verification with Sender's Public Key
In Step 6, the receiver uses the sender's public key to decrypt the digital signature. The public key is freely available — published in the sender's digital certificate or retrieved from a public key directory. Decrypting the signature with the sender's public key recovers the original digest that the sender computed in Step 2 and encrypted with their private key in Step 3. In Step 7, the receiver compares the two digests: the one recovered by decrypting the signature (what the sender computed), and the one independently computed by the receiver (what arrived in the message). If the two digests match, the verification succeeds — proving two things simultaneously: the message came from the purported sender (only they could have produced a signature decryptable by their public key) and the message has not been altered in transit (any modification would have changed the receiver's hash, producing a mismatch).
What Verification Proves
A successful digital signature verification provides three security properties at once. Authentication: the message came from the entity that holds the private key corresponding to the verified public key. Integrity: the message content was not modified between signing and verification — the hash match is mathematical proof of this. Non-repudiation: the signer cannot later deny having signed the message, because the signature could only have been produced by their private key — a key that only they possess. These three properties together are what make digital signatures the mechanism of choice for high-risk ecommerce transactions: software distribution where the recipient must be certain the code has not been tampered with, financial instrument signing, and legal document authentication.
Authentication Methods in 2026 ecommerce
Password-Based Authentication — Baseline and Weaknesses
Password-based authentication — a username and password checked against a stored credential database — is the baseline authentication mechanism for ecommerce customer accounts. When a customer logs into an ecommerce platform such as Amazon or eBay to make a purchase, they provide their username and password; the platform checks these credentials against its records to verify the customer is the legitimate account holder. Password authentication is ubiquitous but has well-documented weaknesses: passwords are reused across sites (enabling credential stuffing), phished through fake login pages, stolen in database breaches, and shared — none of which are detectable by the authentication system. Password authentication alone is no longer considered sufficient for ecommerce accounts with stored payment methods.
Multi-Factor Authentication (MFA) — TOTP, Push, SMS
Multi-factor authentication adds a second verification step after the password, requiring the customer to prove possession of a second factor that the attacker does not have even if they have the correct password. Three MFA mechanisms are commonly deployed in ecommerce. TOTP (Time-based One-Time Password) generates a six-digit code that changes every 30 seconds using a shared secret stored in an authenticator app (Google Authenticator, Authy, Microsoft Authenticator) — the customer enters the current code alongside their password. Push notification authentication sends an approval request to the customer's registered mobile device — the customer taps Approve to confirm the login. SMS authentication sends a one-time code via text message — widely deployed but considered the weakest MFA form because SIM-swapping attacks can redirect SMS to an attacker's phone. Authenticator app TOTP is the current recommended standard for ecommerce MFA; SMS is acceptable only as a fallback.
Passkeys — FIDO2/WebAuthn Replacing Passwords
Passkeys represent the most significant shift in ecommerce customer authentication since the introduction of TLS. A passkey is a FIDO2/WebAuthn credential — a device-bound cryptographic key pair generated by the customer's device. The private key is stored in the device's secure enclave (a hardware security module built into modern smartphones and laptops) and never transmitted. The public key is registered with the merchant. At login, the merchant sends a cryptographic challenge; the device signs the challenge with the private key after verifying the customer's identity through biometrics (fingerprint or face recognition) or device PIN. The signed challenge is returned and verified with the public key.
Passkeys defeat the three primary weaknesses of password authentication simultaneously: they cannot be phished (the key pair is bound to the specific merchant's domain), cannot be credential-stuffed (no shared secret is stored on the server), and cannot be intercepted (the private key never leaves the device). Major ecommerce platforms including Amazon, eBay, Shopify, and PayPal have deployed passkey support as of 2024-2025.
Passkeys defeat the three primary weaknesses of password authentication simultaneously: they cannot be phished (the key pair is bound to the specific merchant's domain), cannot be credential-stuffed (no shared secret is stored on the server), and cannot be intercepted (the private key never leaves the device). Major ecommerce platforms including Amazon, eBay, Shopify, and PayPal have deployed passkey support as of 2024-2025.
Certificate-Based Authentication — Mutual TLS
In standard TLS, only the server presents a certificate — the client (customer's browser) verifies the server's identity but the server does not cryptographically verify the client's identity. Mutual TLS (mTLS) requires both parties to present certificates, enabling the server to cryptographically authenticate the client. mTLS is primarily used in B2B ecommerce API integrations — between merchants and payment processors, between suppliers and procurement systems, between logistics APIs and order management platforms — where machine-to-machine authentication requires stronger guarantees than API keys or OAuth tokens provide. mTLS is not typically used for B2C customer authentication because it requires the customer to install a client certificate, which is operationally impractical at consumer scale.
Biometric Authentication — Device-Bound Verification
Biometric authentication — fingerprint recognition, facial recognition, and voice recognition — is deployed in ecommerce primarily as the unlock mechanism for passkeys and digital wallets rather than as a standalone authentication method. When a customer pays with Apple Pay or Google Pay, biometric verification (Face ID, Touch ID) unlocks the digital wallet and authorizes the payment — the biometric data never leaves the device; it is used locally to unlock the private key stored in the secure enclave. This architecture means biometric authentication inherits the security properties of the underlying cryptographic mechanism (FIDO2/WebAuthn for passkeys, EMV tokenization for digital wallets) rather than transmitting biometric data to the merchant's server, which would create a new category of sensitive data breach risk.
Certification — TLS Certificates and Certificate Authorities
What a TLS Certificate Contains
A TLS certificate is an X.509 digital document that contains the certificate holder's public key, the domain name the certificate is valid for, the certificate's validity period (typically one year), the name of the Certificate Authority that issued and signed the certificate, and the CA's digital signature over all the above. The CA's signature is the element that makes the certificate trusted: browsers maintain a built-in list of trusted root CAs, and any certificate signed by one of those roots (directly or through a chain of intermediate CAs) is accepted as valid. The combination of the domain name binding and the CA signature means that a valid certificate proves both that the site is operated by someone who controls the domain and that a trusted third party has verified that claim.
The Certificate Authority Chain of Trust
The CA hierarchy operates as a chain of trust from root CAs through intermediate CAs to end-entity certificates. Root CA certificates are self-signed and embedded in operating systems and browsers during installation — they are the ultimate trust anchors. Intermediate CAs are signed by root CAs; end-entity certificates (the ones that ecommerce sites use) are signed by intermediate CAs. This three-level structure means root CAs do not sign end-entity certificates directly, reducing the risk from a compromised intermediate CA — if an intermediate CA is compromised, its certificates can be revoked without affecting the root CA or other intermediate CAs in the hierarchy. Major root CAs include DigiCert, Sectigo, GlobalSign, and Let's Encrypt (which provides free domain-validated certificates that have become the standard for most ecommerce sites).
Certificate Revocation — CRL and OCSP
When a certificate's private key is compromised, the certificate must be revoked before its expiration date to prevent an attacker from using it. Two revocation mechanisms are in use. Certificate Revocation Lists (CRLs) are periodically published lists of revoked certificate serial numbers — browsers download and check the list. Online Certificate Status Protocol (OCSP) allows browsers to query the CA in real time about a specific certificate's revocation status — faster and more current than CRLs but dependent on the OCSP responder being available. OCSP Stapling is the modern preferred mechanism: the server itself periodically fetches and caches a signed OCSP response from the CA and includes it in the TLS handshake, eliminating the browser's need to contact the CA separately and improving handshake performance.
Certificate Transparency — Public Audit Logs
Certificate Transparency (CT) is a public logging system that requires CAs to submit all issued certificates to publicly auditable logs. Any certificate not recorded in at least two CT logs is rejected by Chrome and other major browsers. CT enables domain owners to monitor all certificates issued for their domains — detecting unauthorized certificate issuance (a CA fraudulently issuing a certificate for a domain it has not verified) quickly enough to take action before an attacker can exploit it. CT logs are the technical foundation for detecting and responding to the CA compromises and mis-issuances that have historically enabled sophisticated MitM attacks against ecommerce sites.
Authentication in High-Risk ecommerce Transactions
Digital Signatures for Software Distribution
Software distributed through ecommerce channels — operating system updates, application downloads, firmware updates for IoT devices — must be digitally signed to allow recipients to verify that the software has not been tampered with between publication and installation. The publisher signs the software package with their code-signing private key; the installation system verifies the signature with the publisher's public key (obtained from their code-signing certificate) before executing any code. An invalid or absent signature causes the installation to fail or trigger a security warning. Code signing is mandatory for software distributed through major platform stores (Apple App Store, Google Play, Microsoft Store) and is increasingly required for executable files on Windows and macOS even outside of store distribution.
EMV 3D Secure — Risk-Based Authentication for Payments
EMV 3D Secure (3DS2) is the payment industry's standard for authenticating cardholders in card-not-present transactions — the category that encompasses all ecommerce purchases. 3DS2 operates as a real-time risk assessment layer: the merchant passes transaction data to the card network's 3DS server, which applies machine learning models to assess fraud risk based on device fingerprint, transaction history, IP geolocation, browser characteristics, and behavioral signals. Low-risk transactions are approved silently (frictionless flow — no customer interaction required). High-risk transactions trigger a step-up authentication challenge — a one-time code, a push notification to the banking app, or biometric verification. 3DS2's ability to distinguish low-risk from high-risk transactions and apply proportionate authentication is what makes it more effective than blanket MFA for payment authentication.
Strong Customer Authentication (SCA) under PSD2
The European Payment Services Directive 2 (PSD2) mandates Strong Customer Authentication for most electronic payments initiated by EU customers — regardless of whether the merchant is based in the EU. SCA requires authentication using at least two of three factors: something the customer knows (password, PIN), something the customer has (mobile device, hardware token), and something the customer is (biometric). Transactions above €30 generally require SCA unless they qualify for an exemption (low-value transactions under €30, merchant-initiated transactions with prior authorization, low-risk transactions below issuer fraud thresholds). For ecommerce merchants selling to EU customers, SCA compliance is a legal requirement — non-compliant transactions will be declined by EU-issuing banks. 3DS2 is the primary technical mechanism through which SCA is implemented for card-based ecommerce payments.
In the next lesson, you will identify various certification methods.
In the next lesson, you will identify various certification methods.