| Lesson 2 | Purposes of security |
| Objective | Identify the need for secure electronic transactions. |
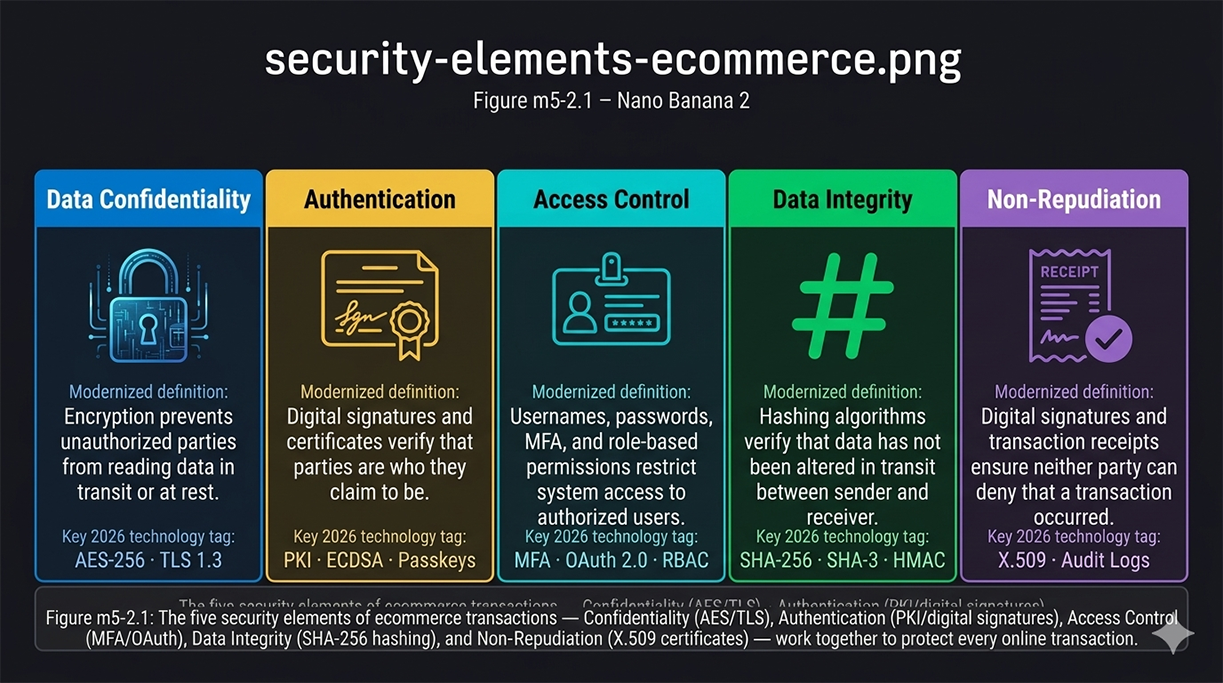
Secure Electronic Transactions (Five Security Elements of ecommerce)
Every ecommerce transaction — from browsing a product page through completing checkout — passes through multiple security layers that are largely invisible to the consumer but essential to the integrity of the exchange. When a customer enters a credit card number, selects a shipping address, and clicks "Place Order," the platform must simultaneously protect that data from interception, verify that both parties are who they claim to be, prevent unauthorized access to backend systems, guarantee that the transaction details arrive unaltered, and create an irrefutable record that the transaction occurred. These five requirements correspond exactly to the five security elements that underpin every secure electronic transaction system: data confidentiality, authentication, access control, data integrity, and non-repudiation. Understanding why each element is necessary — and what happens when any one of them fails — is the foundation for understanding how ecommerce security is designed and implemented.
The Five Security Elements — Figure m5-2.1
In ecommerce, security involves five essential purposes that work together to protect every transaction. No single element is sufficient alone — a system with strong confidentiality but weak authentication can be breached by impersonation; a system with strong authentication but no integrity verification can be manipulated in transit. Figure m5-2.1 presents all five elements and their 2026 technology implementations as a unified framework.
Zone-by-Zone Walkthrough
Zone 1 — Data Confidentiality (AES-256 and TLS 1.3)
Data confidentiality ensures that sensitive information is accessible only to the intended parties — that payment credentials, personal addresses, and account details cannot be read by anyone who intercepts the data stream between the customer's browser and the merchant's server. The degree of confidentiality required varies by data type: a private B2B contract negotiated in real time between two parties demands the highest level of encryption protection, while publicly available information such as weather data or stock prices requires minimal confidentiality because its exposure causes no harm.
In practice, confidentiality is implemented through encryption — the transformation of readable plaintext into ciphertext that is unintelligible without the correct decryption key. The current standard for symmetric encryption is AES-256 (Advanced Encryption Standard with a 256-bit key), which is used to encrypt the body of every HTTPS session. TLS 1.3 (Transport Layer Security version 1.3) is the protocol that establishes the encrypted channel between the browser and the server — negotiating cipher suites, authenticating the server's certificate, and deriving the session keys that AES-256 will use. Older protocols (SSL, TLS 1.0, TLS 1.1) are deprecated and disabled on all modern ecommerce platforms due to known vulnerabilities. Any ecommerce platform that cannot demonstrate TLS 1.3 support fails its customers' basic confidentiality requirement.
In practice, confidentiality is implemented through encryption — the transformation of readable plaintext into ciphertext that is unintelligible without the correct decryption key. The current standard for symmetric encryption is AES-256 (Advanced Encryption Standard with a 256-bit key), which is used to encrypt the body of every HTTPS session. TLS 1.3 (Transport Layer Security version 1.3) is the protocol that establishes the encrypted channel between the browser and the server — negotiating cipher suites, authenticating the server's certificate, and deriving the session keys that AES-256 will use. Older protocols (SSL, TLS 1.0, TLS 1.1) are deprecated and disabled on all modern ecommerce platforms due to known vulnerabilities. Any ecommerce platform that cannot demonstrate TLS 1.3 support fails its customers' basic confidentiality requirement.
Zone 2 — Authentication (PKI, Digital Signatures, Passkeys)
Authentication verifies that the entities participating in a transaction are who they claim to be. The internet is by nature an anonymous medium — without authentication mechanisms, a customer cannot confirm that the website accepting their payment is the legitimate merchant rather than a phishing site, and the merchant cannot confirm that the person submitting payment is the authorized cardholder rather than a fraudster using stolen credentials. Authentication is therefore tantamount in all high-value transactions, high-volume transaction environments, and any exchange involving sensitive personal or financial information.
Server-side authentication — confirming that the merchant's website is legitimate — is accomplished through digital certificates issued by trusted Certificate Authorities (CAs). When a browser connects to an HTTPS site, the server presents its X.509 certificate; the browser verifies the certificate's signature against the CA's public key and confirms that the domain matches the certificate's subject. This chain of trust — from the root CA through intermediate CAs to the server certificate — is the foundation of Public Key Infrastructure (PKI). Client-side authentication — confirming that the customer is the authorized account holder — is implemented through username/password credentials reinforced by multi-factor authentication (MFA), and increasingly through passkeys (FIDO2/WebAuthn), which replace passwords entirely with device-bound cryptographic key pairs. ECDSA (Elliptic Curve Digital Signature Algorithm) is the current standard for the digital signature operations that underpin both server certificates and passkey authentication.
Server-side authentication — confirming that the merchant's website is legitimate — is accomplished through digital certificates issued by trusted Certificate Authorities (CAs). When a browser connects to an HTTPS site, the server presents its X.509 certificate; the browser verifies the certificate's signature against the CA's public key and confirms that the domain matches the certificate's subject. This chain of trust — from the root CA through intermediate CAs to the server certificate — is the foundation of Public Key Infrastructure (PKI). Client-side authentication — confirming that the customer is the authorized account holder — is implemented through username/password credentials reinforced by multi-factor authentication (MFA), and increasingly through passkeys (FIDO2/WebAuthn), which replace passwords entirely with device-bound cryptographic key pairs. ECDSA (Elliptic Curve Digital Signature Algorithm) is the current standard for the digital signature operations that underpin both server certificates and passkey authentication.
Zone 3 — Access Control (MFA, OAuth 2.0, RBAC)
Access control governs which users, services, and systems can access which resources on the ecommerce platform. Where authentication answers the question "who are you?", access control answers the question "what are you allowed to do?" A customer who has been authenticated as a valid account holder should be able to view their own order history and update their own payment methods — but not access another customer's account, modify product prices, or read the merchant's financial reports. An employee in a fulfillment role should be able to update order shipping status but not issue refunds or access customer payment credentials. Access control enforces these boundaries.
Modern access control in ecommerce systems is implemented through three complementary mechanisms. Role-Based Access Control (RBAC) assigns permissions to roles (customer, fulfillment staff, finance administrator, system administrator) and assigns users to those roles — a user inherits the permissions of their role rather than receiving individual permissions. OAuth 2.0 is the authorization framework used when an ecommerce platform delegates access to third-party services — when a merchant's platform connects to a shipping API, an accounting system, or a social media integration, OAuth 2.0 governs what data that third-party service can access and for how long. MFA adds a second verification step at the authentication boundary, ensuring that even if a user's password is compromised through credential stuffing or phishing, the attacker cannot complete login without the second factor. File transfer access controls — historically managed through FTP username and host restrictions — are now implemented through SFTP (SSH File Transfer Protocol) or FTPS (FTP over TLS), with FTP itself deprecated due to its transmission of credentials in plaintext.
Modern access control in ecommerce systems is implemented through three complementary mechanisms. Role-Based Access Control (RBAC) assigns permissions to roles (customer, fulfillment staff, finance administrator, system administrator) and assigns users to those roles — a user inherits the permissions of their role rather than receiving individual permissions. OAuth 2.0 is the authorization framework used when an ecommerce platform delegates access to third-party services — when a merchant's platform connects to a shipping API, an accounting system, or a social media integration, OAuth 2.0 governs what data that third-party service can access and for how long. MFA adds a second verification step at the authentication boundary, ensuring that even if a user's password is compromised through credential stuffing or phishing, the attacker cannot complete login without the second factor. File transfer access controls — historically managed through FTP username and host restrictions — are now implemented through SFTP (SSH File Transfer Protocol) or FTPS (FTP over TLS), with FTP itself deprecated due to its transmission of credentials in plaintext.
Zone 4 — Data Integrity (SHA-256, SHA-3, HMAC)
Data integrity ensures that transaction data has not been modified in transit between sender and receiver. Without integrity verification, a man-in-the-middle attacker who has positioned themselves between the customer's browser and the merchant's server could alter the transaction details — changing the payment amount, substituting a different shipping address, or modifying the items ordered — without either party detecting the manipulation. The customer would believe they ordered one thing; the merchant would process a different order; and neither would know until after the transaction completed.
Integrity is verified through cryptographic hashing — a mathematical algorithm that produces a fixed-length output (the hash or message digest) from an input of any length. The same input always produces the same hash; any change to the input — even a single bit — produces a completely different hash. The sender computes a hash of the data before transmission and transmits it alongside the data; the receiver recomputes the hash from the received data and compares it to the transmitted hash. A match confirms that the data arrived unaltered. The current standard hashing algorithms are SHA-256 (part of the SHA-2 family) and SHA-3 — older algorithms including MD5 and SHA-1 are deprecated due to discovered collision vulnerabilities that allow attackers to craft two different inputs that produce the same hash. HMAC (Hash-based Message Authentication Code) combines hashing with a secret key, providing both integrity verification and authentication of the message source in a single operation.
Integrity is verified through cryptographic hashing — a mathematical algorithm that produces a fixed-length output (the hash or message digest) from an input of any length. The same input always produces the same hash; any change to the input — even a single bit — produces a completely different hash. The sender computes a hash of the data before transmission and transmits it alongside the data; the receiver recomputes the hash from the received data and compares it to the transmitted hash. A match confirms that the data arrived unaltered. The current standard hashing algorithms are SHA-256 (part of the SHA-2 family) and SHA-3 — older algorithms including MD5 and SHA-1 are deprecated due to discovered collision vulnerabilities that allow attackers to craft two different inputs that produce the same hash. HMAC (Hash-based Message Authentication Code) combines hashing with a secret key, providing both integrity verification and authentication of the message source in a single operation.
Zone 5 — Non-Repudiation (X.509 Certificates, Audit Logs)
Non-repudiation is proof that a specific transaction was conducted between two specific parties — preventing either the merchant or the customer from later denying that the transaction occurred. Without non-repudiation, a customer could claim they never placed an order after receiving the goods, or a merchant could claim a payment was never received. Non-repudiation is the legal and technical foundation of dispute resolution in ecommerce.
Non-repudiation is implemented through digital signatures applied to transaction records. When a customer completes a purchase, the platform generates a cryptographically signed transaction receipt — a record that combines the transaction details with a digital signature created using the merchant's private key. Because only the holder of the private key can generate that signature, and the signature can be verified by anyone with the corresponding public key (embedded in the merchant's X.509 certificate), the receipt constitutes mathematical proof that the merchant's system processed the specific transaction. The customer's acceptance of the transaction — recorded with a timestamp and session identifier — completes the non-repudiation chain. Immutable audit logs maintained by the payment processor and gateway provide a third-party corroborating record. In payment card disputes, the combination of the gateway's transaction log, the merchant's signed receipt, and the card network's authorization record makes it computationally infeasible for either party to credibly deny the transaction.
Non-repudiation is implemented through digital signatures applied to transaction records. When a customer completes a purchase, the platform generates a cryptographically signed transaction receipt — a record that combines the transaction details with a digital signature created using the merchant's private key. Because only the holder of the private key can generate that signature, and the signature can be verified by anyone with the corresponding public key (embedded in the merchant's X.509 certificate), the receipt constitutes mathematical proof that the merchant's system processed the specific transaction. The customer's acceptance of the transaction — recorded with a timestamp and session identifier — completes the non-repudiation chain. Immutable audit logs maintained by the payment processor and gateway provide a third-party corroborating record. In payment card disputes, the combination of the gateway's transaction log, the merchant's signed receipt, and the card network's authorization record makes it computationally infeasible for either party to credibly deny the transaction.
Why Secure Transactions Are Non-Negotiable
Consumer Trust and Cart Abandonment
Consumer hesitation about online payment security is not irrational — it is a rational response to a real threat environment. Cart abandonment studies consistently identify payment security concerns as a leading cause of incomplete transactions. Visible security indicators — the padlock icon in the browser address bar, "Secure Checkout" labeling, recognized payment logos — directly influence purchase completion rates. Merchants who fail to display these signals lose conversions at the final step of the funnel, after bearing the full cost of customer acquisition. The investment in robust security infrastructure pays a direct return through improved conversion rates and repeat purchase rates, because customers who trust a merchant's security return to buy again.
Financial Fraud — CNP Fraud, Account Takeover, 3D Secure
Card-not-present (CNP) fraud — fraudulent use of a card number without the physical card — is the dominant form of ecommerce payment fraud. Unlike point-of-sale fraud, CNP fraud requires only the card number, expiration date, and CVV, all of which are obtained through data breaches, phishing, and skimming attacks on ecommerce checkout pages. Account takeover attacks use credential stuffing — automated testing of username/password combinations from breached databases — to access legitimate customer accounts and make purchases using stored payment methods. EMV 3D Secure (3DS2) is the payment industry's primary defense against CNP fraud: it adds a real-time risk assessment layer to every card transaction, requiring additional authentication (a one-time code, biometric confirmation, or in-app approval) for transactions that the issuing bank's fraud model flags as high-risk. Tokenization — replacing the actual card number with a payment-network-issued token that is valid only for a specific merchant — prevents card data stored by the merchant from being useful to attackers even if the storage system is breached.
Business Reputation and Revenue Impact
A single significant data breach — the exposure of customer payment credentials, personal data, or account information — produces costs that extend far beyond the immediate remediation expense. Regulatory fines under PCI DSS, GDPR, and CCPA can reach millions. Legal liability from affected customers compounds the financial exposure. Reputational damage — amplified by media coverage and social media — reduces customer acquisition rates and increases churn among existing customers for months or years following the incident. Research consistently shows that a meaningful percentage of customers who learn that a merchant has suffered a data breach do not return to that merchant. For ecommerce businesses operating on thin margins, the revenue impact of sustained churn following a breach can exceed the direct breach cost.
Regulatory Compliance
PCI DSS — Payment Card Industry Requirements
The Payment Card Industry Data Security Standard (PCI DSS) is the security framework established by the major card networks — Visa, Mastercard, American Express, Discover, and JCB — to govern how merchants, payment processors, and service providers handle cardholder data. PCI DSS version 4.0, current as of 2026, defines requirements across twelve domains: network security, default configuration management, cardholder data protection, encrypted transmission, malware protection, secure system development, access restriction, authentication management, physical access control, activity logging, security testing, and information security policy. Merchants are assessed at one of four compliance levels based on annual transaction volume; the highest-volume merchants undergo annual on-site assessments by a Qualified Security Assessor (QSA), while lower-volume merchants complete annual Self-Assessment Questionnaires (SAQs). Non-compliance results in escalating fines, increased interchange rates, and ultimately loss of the ability to accept card payments.
GDPR and CCPA — Personal Data Protection
The General Data Protection Regulation (GDPR) governs the collection, processing, and storage of personal data for individuals in the European Union — applicable to any ecommerce merchant who sells to EU customers regardless of where the merchant is based. GDPR requires lawful basis for data processing, data minimization, the right of individuals to access and delete their data, breach notification within 72 hours, and privacy-by-design in system architecture. The California Consumer Privacy Act (CCPA) and its amendment the CPRA impose similar requirements for California residents — the right to know what data is collected, the right to opt out of data sale, and the right to deletion. For ecommerce merchants, GDPR and CCPA compliance requires audit trails of customer data collection and processing, documented data retention policies, secure deletion procedures, and breach detection and notification capabilities — all of which overlap directly with the technical security controls the five security elements require.
Merchant Obligations and Compliance Scope
The practical compliance scope for a typical ecommerce merchant depends on how payment processing is implemented. Merchants who redirect customers to a hosted payment page operated by a gateway (Stripe Checkout, PayPal Standard, Square) never see cardholder data and qualify for the simplest SAQ-A self-assessment — the gateway assumes responsibility for PCI DSS compliance for the payment processing environment. Merchants who embed payment forms on their own pages using JavaScript iframes from the gateway qualify for SAQ-A-EP. Merchants who process payment data directly on their own servers face the most complex compliance requirements. The security architecture decision — hosted redirect versus embedded form versus direct processing — is therefore a compliance decision as much as a technical one.
Enabling Global and Scalable Commerce
Cross-Border Payment Security
ecommerce operates across borders with customers in multiple countries, currencies, and regulatory jurisdictions. A transaction from a UK customer paying in GBP to a US merchant settling in USD passes through the customer's issuing bank, a currency conversion service, the card network's international routing infrastructure, and the merchant's acquiring bank — each step a potential point of interception or manipulation. The five security elements apply at every point in this chain: TLS encryption protects data in transit across each network boundary; PKI authentication verifies each participating institution's identity; access controls govern which systems can initiate or modify the transaction; integrity hashing detects any alteration at any hop; and the complete transaction record provides non-repudiation across all parties regardless of jurisdiction.
Modern Gateway Integrations — Stripe, PayPal, Adyen
The major payment gateways — Stripe, PayPal, and Adyen — provide pre-built security infrastructure that ecommerce merchants integrate via API. Each gateway handles PCI DSS compliance for the payment processing environment, implements tokenization to prevent raw card data from reaching the merchant's systems, supports 3D Secure 2.0 for dynamic authentication, and provides real-time fraud scoring using machine learning models trained on global transaction data. For merchants building on modern ecommerce platforms — Shopify, WooCommerce, BigCommerce, Magento 2 — native gateway integrations provide the five security elements out of the box without requiring the merchant to implement cryptographic protocols directly. Headless commerce architectures (Commerce.js, Saleor) and JAMstack ecommerce (Next.js Commerce) expose payment security through the same gateway APIs, applying the same security elements regardless of the frontend rendering approach. The security framework is platform-agnostic; the five elements are invariant across every implementation.
In the next lesson, you will learn about encryption and decryption.
Security Purpose - Quiz
Click the Quiz link below to test your understanding of the purposes of security.
Security Purpose - Quiz
Security Purpose - Quiz
[1] Access control: Access control governs what resources a user or service may access on the system or network. It protects against the unauthorized use of resources.